
Embracing technology has become essential for businesses to enhance efficiency, reduce costs, and streamline operations.
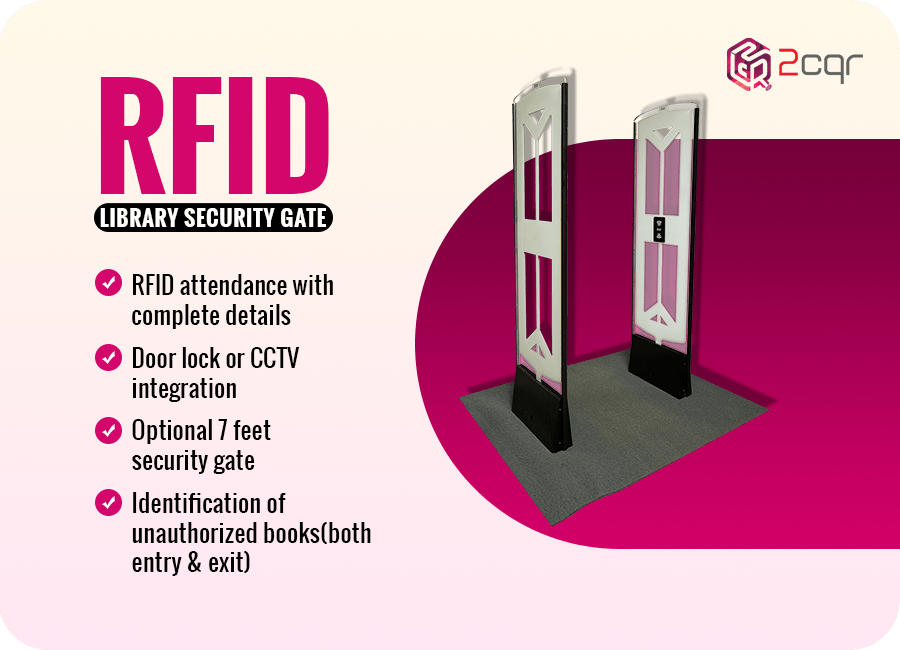
This holds true for libraries as well, where the adoption of RFID-based library management systems is gaining significance.
Though RFID technology in libraries offers efficient and rapid solutions, cost and security remain as important considerations in implementing RFID for library management.
Let’s delve deeper into
5 elements that will help you to enhance security of data in RFID tags

Encryption: Ensure that the data transmitted between RFID tags and readers is encrypted to prevent the valuable data can be accessed by unauthorized personnel & avoid unnecessary complications.
It would be always ideal to follow industry-standard encryption protocols to secure the communication and make your library management efficient and secured with RFID technology in libraries.
Access Control: Limiting the access to less number of people to read and write the data on RFID tags is much needed to make sure that only authorised personnel or systems can interact with the tags.
Making use of authentication methods like keeping strong passwords, access cards, or biometrics to control access and improve the standard of security.
Privacy Protection: Consider the privacy of library users while implementing RFID technology in libraries . Ensure that personally identifiable information (PII) is not stored on RFID tags or is encrypted if necessary to maintain the confidentiality of users data and gain trust. Anonymise or pseudonyms data whenever possible to protect user privacy.
Data Retention Policies: Establish clear data retention policies to secure the data programmed in RFID tags. Determine how long the data should be stored and when it should be securely deleted.
By implementing proper data retention practices, you can reduce the risk of unnecessary data breaches that spoil your reputation.
Vendor Selection: While choosing the RFID Suppliers for libraries, its very much important to understand the security standards followed by them in designing and manufacturing RFID tags rather than just giving priority to their reputation.
Cross check whether the respective vendors act in accordance with the compliance standards or not to take the final decision


Thats why you have to take security measure to protect the confidentiality of the data.